Internet of Things (IoT) devices and their functionalities have benefited from the introduction of serverless computing into the IoT landscape. Instead of manufacturers hosting and maintaining their own servers to develop and support these devices, cloud providers allocate machine resources as needed based on the companys’ computational needs. This ensures less downtime for users of IoT devices, lower costs for the manufacturers, and quicker deployments of new applications.
But serverless computing has created new avenues for attackers to conceal their activities within legitimate workflows. Neither traditional approaches to system auditing nor commercial serverless security products provide the transparency needed to accurately track these novel threats.
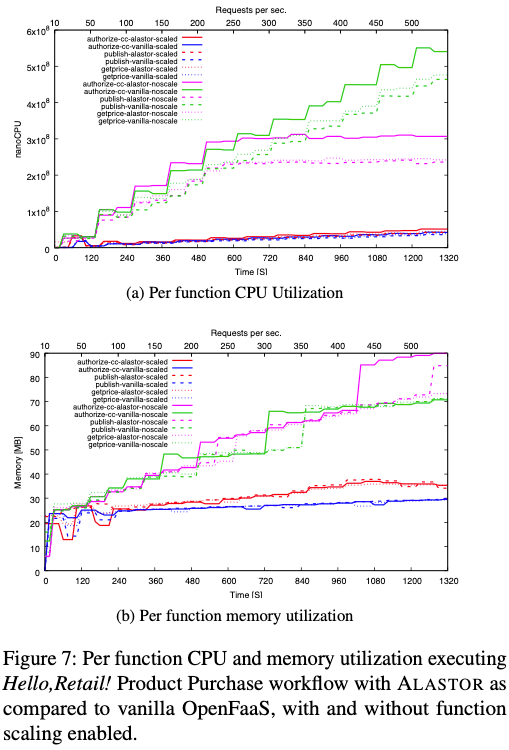
ALASTOR is a provenance-based auditing framework that enables precise tracing of suspicious events in serverless applications. By reconstructing the attack path in full detail, ALASTOR makes it easy to diagnose the intrusion and determine its impacts.
To learn more, check out the publication!
Datta, Pubali, Isaac Polinsky, Muhammad Adil Inam, Adam Bates, and William Enck. “ALASTOR: Reconstructing the Provenance of Serverless Intrusions,” 2022. https://www.usenix.org/conference/usenixsecurity22/presentation/datta.








Leave a comment