Mobile devices have become an indispensable component of modern life. With high storage capacity, these devices can store large amounts of sensitive personal data, making them a high-value target for data theft, and a valuable source of forensic data for law-enforcement agencies.
Over the past several years, device and cloud service providers have deployed a number of advanced cryptographic features intended to protect data on mobile devices, including in settings where an attacker has physical access to a device. Many of these cryptographic features are drawn from the research literature, and have been adapted to these new settings, some of which include novel challenges which have not been addressed in literature.
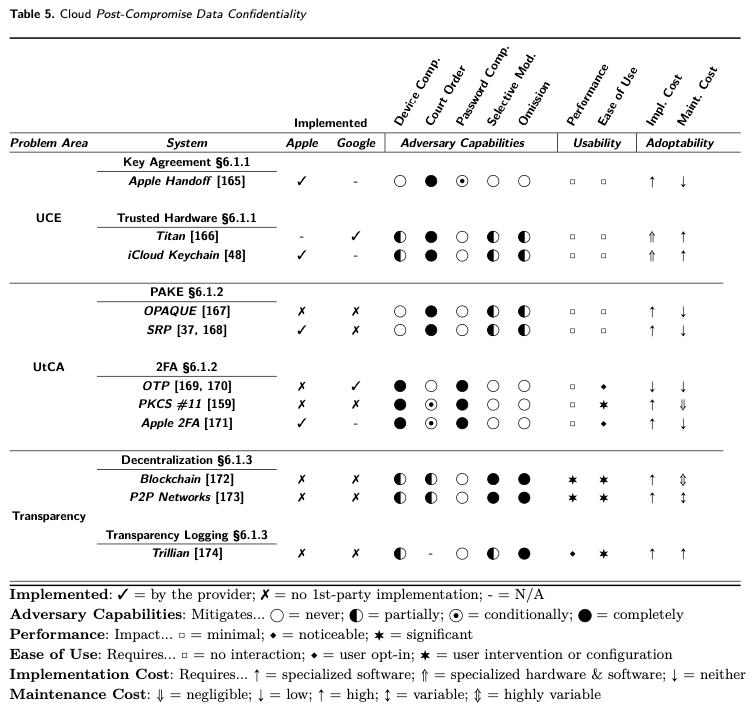
In this work, we outline those novel challenges, and systematize the known approaches to securing user data against extraction attacks. We evaluate the existing literature for securing devices against data extraction adversaries with powerful capabilities, including access to devices and to the cloud services they rely on. Our work proposes a methodology that researchers can use to analyze cryptographic data confidentiality for mobile devices. We then analyze existing mobile device confidentiality measures to identify research areas that have not received proper attention from the community and represent opportunities for future research.
To learn more, check out the paper below! You can find more of the team’s work on comparing the state of the art in data security on mobile devices here.
Zinkus, M., Jois, T. M., & Green, M. (2022). SoK: Cryptographic Confidentiality of Data on Mobile Devices. Proceedings on Privacy Enhancing Technologies, 2022, 586–607. https://doi.org/10.2478/popets-2022-0029








Leave a comment