The most common forms of authentication are passwords, potentially used in combination with a second factor such as a hardware token or mobile app (i.e., two-factor authentication). These approaches emphasize a one-time, initial authentication. Recent work has explored how to provide passive, continuous authentication and/or automatic de-authentication by correlating user movements and inputs with actions observed in an application (e.g., a web browser). The issue with indefinite trust goes beyond user authentication; consider devices that pair via Bluetooth.
The increased adoption of IoT devices and reports of inadequacy of their security makes indefinite trust of devices problematic. The reality of ubiquitous connectivity and frequent mobility gives rise to a myriad of opportunities for devices to be compromised. Thus, we argue that one-time, single-factor, device-to-device authentication (i.e., an initial pairing) is not enough, and that there must exist some mechanism to frequently (re-)verify the authenticity of devices and their connections.
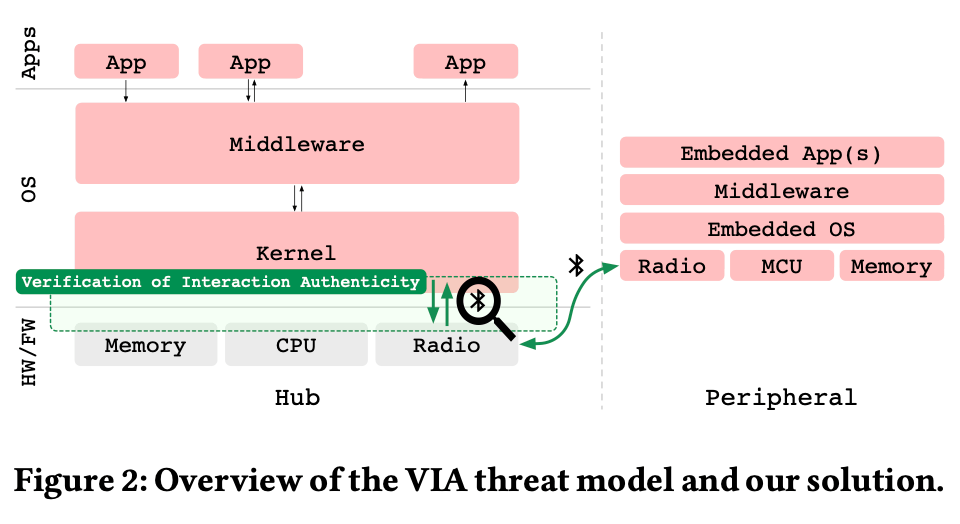
In this paper we propose a device-to-device recurring authentication scheme – Verification of Interaction Authenticity (VIA) – that is based on evaluating characteristics of the communications (interactions) between devices. We adapt techniques from wireless traffic analysis and intrusion detection systems to develop behavioral models that capture typical, authentic device interactions (behavior); these models enable recurring verification of device behavior.
To read more, check out the paper here.
Travis Peters, Timothy J. Pierson, Sougata Sen, José Camacho, and David Kotz. Recurring Verification of Interaction Authenticity Within Bluetooth Networks. Proceedings of the ACM Conference on Security and Privacy in Wireless and Mobile Networks (WiSec 2021), pages 192–203. ACM, June 2021. doi:10.1145/3448300.3468287. ©








Leave a comment